The Fatal Flaw of Legacy Thresholds in the Application Layer (Layer 7)
The cybersecurity industry has historically suffered from a paradox: intense DDoS protection inevitably results in degraded user experiences. For over a decade, legacy hardware appliances and static Web Application Firewalls (WAFs) have relied on a blunt methodology known as volumetric rate-limiting. When an influx of traffic breaches a predefined numeric threshold, these archaic systems panic, dropping packets indiscriminately.
This is especially catastrophic against Layer 7 (Application Layer) assaults. Modern attackers do not rely on simple Layer 3 or Layer 4 volumetric floods anymore. Instead, they unleash sophisticated, polymorphic Layer 7 botnets designed specifically to emulate real human browsers, bypass JavaScript challenges, and evade IP-based rate-limits by distributing payloads across millions of residential proxies. Relying on static, legacy rules against these synthetic threats locks out legitimate customers, paralyzes API endpoints, and inflicts the exact downtime the attack intended to cause.
At CoreTech, we engineered a radical departure. To combat these advanced Layer 7 threats, we built CoreDetection™—a deep Machine Learning (ML) engine driven by robust Artificial Intelligence, operating entirely at edge wire-speed.
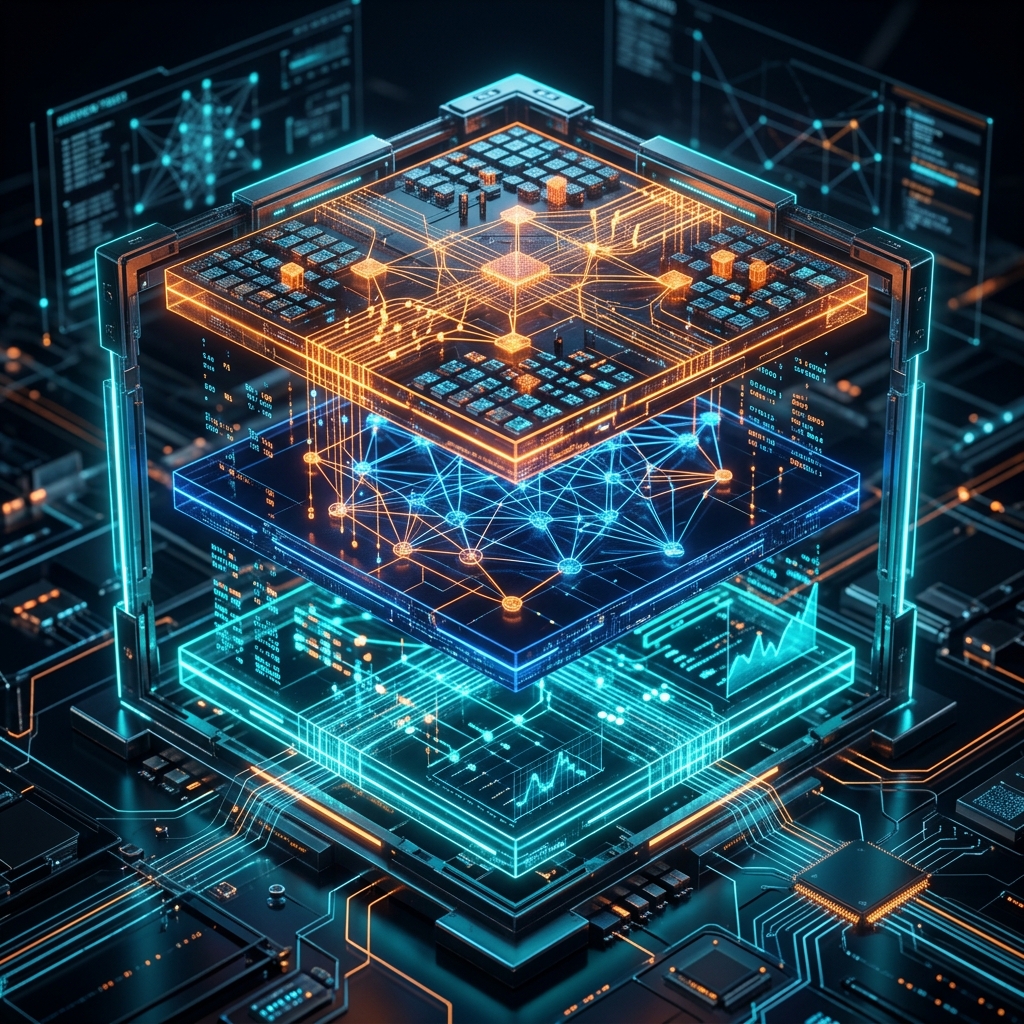
Deconstructing the 3-Tier AI Neural Network
Note: The following architecture refers to the cognitive processing tiers of our AI Engine, distinct from the OSI networking model.
Unlike legacy systems that view traffic through a single, numeric lens, CoreDetection™ utilizes an advanced Deep Machine Learning pipeline. It interrogates high-level application data (HTTP/S headers, TLS handshakes, User-Agent behavior) through a simultaneous, three-dimensional behavioral matrix.
Cognitive Tier 1: Machine Learning Rhythm & Pace Analysis
Legitimate human interaction across an application layer (L7) is inherently chaotic—punctuated by organic latency, mouse movements, and irregular request intervals. Polymorphic botnets, however, operate via programmed loop routines. Tier 1 of our AI engine introduces robust Machine Learning models to analyze 61-second traffic bursts. Instead of counting volume, the AI identifies the highly unnatural, synchronized “rhythm” of distributed proxies striking simultaneously. By learning these synthetic cadence discrepancies, the ML engine tags robotic behavior definitively, no matter how broadly the attacker rotates their IPs.
Cognitive Tier 2: Deep Traffic Fingerprinting
While Tier 1 dictates pace, Tier 2 examines the deep anatomy of the Application Layer payload. Utilizing deep neural networks, this tier intercepts the HTTP/HTTPS payloads and builds complex multidimensional relationships between the Source IPs, geographical dispersion, asymmetric request structures, and TLS fingerprint anomalies. By continuously feeding this data into our unsupervised learning algorithms, the AI maps a structural baseline of your legitimate traffic. If a botnet cluster attempts a stealthy Application Layer attack by forging User-Agents to look like Chrome or Safari, the AI mathematically exposes the deviation in their payload structure in milliseconds.
Cognitive Tier 3: Autonomous Attack Memory and Heuristic Learning
The true brilliance of a Machine Learning-driven network is its infinite capacity to evolve. Tier 3 functions as the omniscient brain of the CoreEdge™ network. When a novel, polymorphic L7 assault is isolated and mitigated, the AI extracts its complex behavioral signature and commits it to global cluster memory. Since our ML models are globally stateful, if that specific botnet matrix attempts to re-engage weeks later—even targeting a totally different CoreTech enterprise client—the Heuristic Learning engine achieves an 85%+ structural pattern match in sub-seconds. It recognizes the threat instantly and blocks it autonomously before the attack can even register on the target servers.
Autonomous Execution and Invisible Defense
The synergy of these three Machine Learning tiers represents a monumental leap in Application Security. When L7 traffic is ingested, the engine aggregates the Rhythm, Fingerprint, and Memory tensors into a definitive AI threat score. Only when the autonomous threshold reaches absolute mathematical certainty (100% confidence) does CoreDetection™ deploy surgical, invisible micro-mitigation to eliminate the botnet traffic.
There are no jarring CAPTCHA walls aggravating real users, no dropped API hooks, and zero false positives. With CoreDetection’s Deep Machine Learning pipeline, you are implementing a cognitive AI network that actively out-thinks, out-learns, and entirely out-maneuvers the most complex Application Layer cyber warfare known today.
Want to see this in action?
Get a live demonstration of CoreTech's DDoS mitigation platform.