The Evolution of the Patient Attack
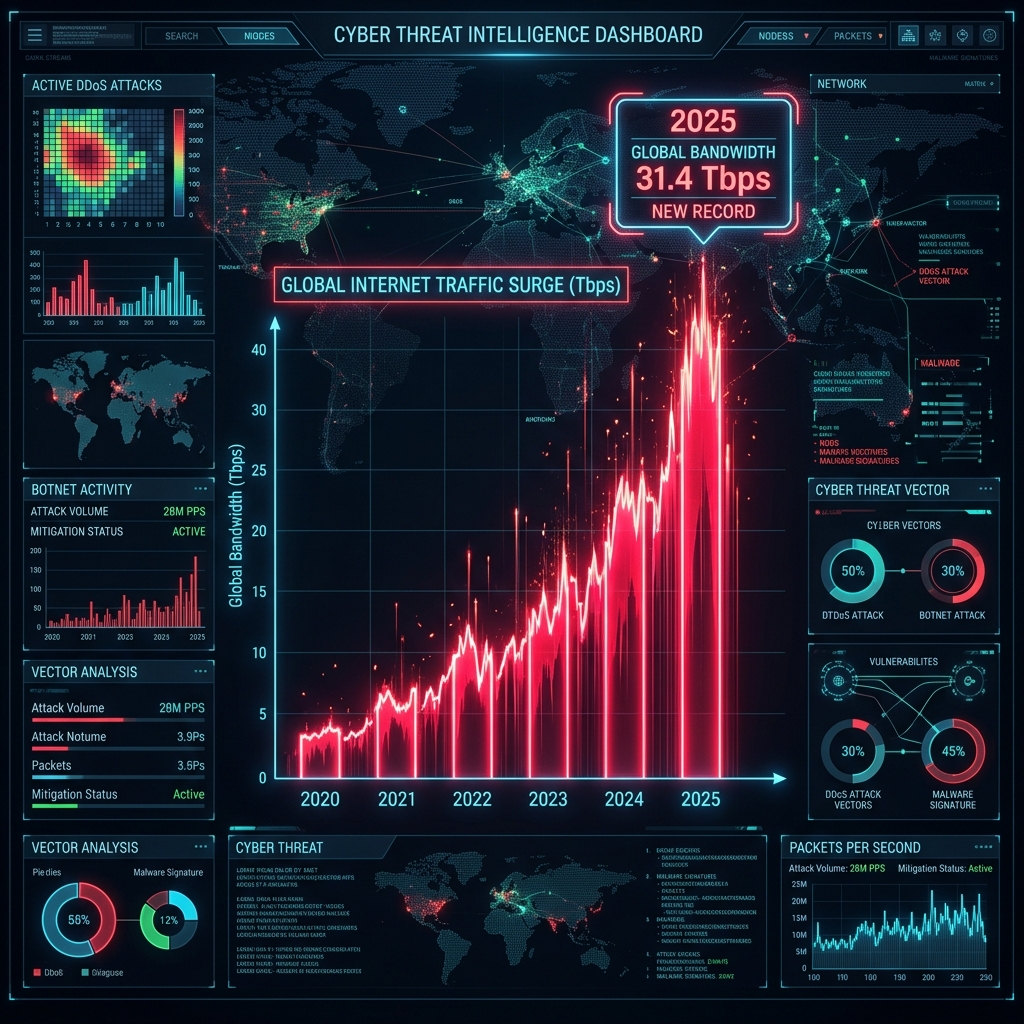
The DDoS landscape has matured dramatically over the past several years. In the early era of volumetric assault campaigns, attackers operated with relative bluntness — activating their full botnet capacity simultaneously and relying on sheer packet volume to overwhelm defenses. Those attacks were easy to see coming. The traffic spike was immediate, obvious, and precisely the kind of pattern that conventional threshold-based alerting systems were designed to detect.
The adversary community learned, adapted, and evolved. The dominant attack methodology favored by sophisticated threat actors in 2026 is fundamentally different in its operational logic. Rather than announcing the assault with an immediate surge, modern attack campaigns employ a calculated escalation strategy — beginning at a volume deliberately calibrated to fall beneath standard detection thresholds, then incrementally increasing pressure over a period of minutes. By the time conventional monitoring systems register the traffic as anomalous, the attack has already consumed significant bandwidth, exhausted upstream session tables, and in many cases caused measurable service degradation that legacy appliances cannot reverse without a full mitigation reset.
CoreEdge was engineered with this adversarial evolution explicitly in mind.
Measuring the Acceleration, Not the Volume
The foundational insight behind CoreEdge’s Velocity Detection capability is a recognition that slow-burn attack campaigns are identifiable long before they reach threatening absolute volumes — if you measure the rate of change in traffic characteristics rather than the characteristics themselves.
Every traffic source flowing through CoreEdge-protected networks is continuously evaluated not just for its current behavior, but for the trajectory of that behavior across a rolling time window. Our Velocity Detection engine monitors the acceleration profile of inbound traffic streams with sub-second granularity. When the velocity of traffic increase from a particular source cluster exceeds the behavioral baseline established for that network segment — even when current absolute volumes remain within normal operating parameters — our engine immediately flags the anomaly and begins applying escalating interception countermeasures.
This is the critical distinction from all legacy threshold-based detection: CoreEdge does not wait for an attack to reach full operational scale before responding. It identifies the attack’s growth trajectory at the earliest possible moment and begins neutralizing it while it is still in its escalation phase. In documented production scenarios, CoreEdge’s Velocity Detection engine has identified and begun mitigating slow-escalation campaigns within 1 to 3 seconds of the first measurable anomalous acceleration — a detection window that occurs minutes before conventional monitoring systems would register any cause for concern.
The Mathematics of Early Interception
The operational significance of this detection window cannot be overstated. Consider the arithmetic of a typical slow-burn campaign against a network protected by a conventional threshold-based mitigation platform. An attacker operating at deliberate escalation pace might require 4 to 8 minutes to bring their assault from initial, below-threshold traffic to the full operational volume that finally triggers a legacy system’s alert and initiates a mitigation response. In that window, the attack has consumed enormous bandwidth, the upstream provider may have initiated emergency route filtering, and service quality has already degraded perceptibly for legitimate users.
Against CoreEdge, the same campaign’s first 3 seconds of anomalous acceleration acceleration is sufficient for our Velocity Detection engine to identify the threat profile, classify the traffic cluster, and begin applying precision interception parameters. The attack never reaches operational scale. The upstream links never see the load. The application servers never register the pressure. The legitimate user experience remains completely unaffected from the first second of the attack to its inevitable collapse as the attacker’s infrastructure encounters CoreEdge’s interception perimeter and achieves zero penetration.
Acceleration Profiling Across the Global Fleet
The velocity awareness architecture within CoreEdge extends beyond individual node monitoring to encompass a globally coordinated acceleration intelligence network. Traffic acceleration patterns identified by CoreEdge nodes at any point in our global fleet are immediately communicated across the entire distributed network. When a slow-escalation campaign is identified against one CoreTech client, the velocity signature of that campaign — its specific acceleration profile, source distribution, and behavioral fingerprint — is instantaneously available to all other nodes in our fleet.
This global velocity intelligence means that an attack campaign that achieves even momentary progression against one node will find every other CoreEdge node in our global fleet pre-calibrated and ready for its arrival. Coordinated multi-target slow-burn campaigns — a growing attack strategy in which threat actors simultaneously escalate against multiple targets to divide attention — encounter not distributed detection uncertainty but a unified, globally coordinated velocity awareness system that responds to all fronts simultaneously.
For organizations whose previous DDoS protection experience has been defined by the reactive scramble of legacy platforms — detecting the attack only after damage has begun, then racing to apply mitigation while under full assault — CoreEdge’s Velocity Detection capability represents a categorically different operating model. One in which the attacker’s campaign is identified and neutralized while they believe they are still safely below the detection horizon.
Want to see this in action?
Get a live demonstration of CoreTech's DDoS mitigation platform.