Every Weapon Leaves a Mark
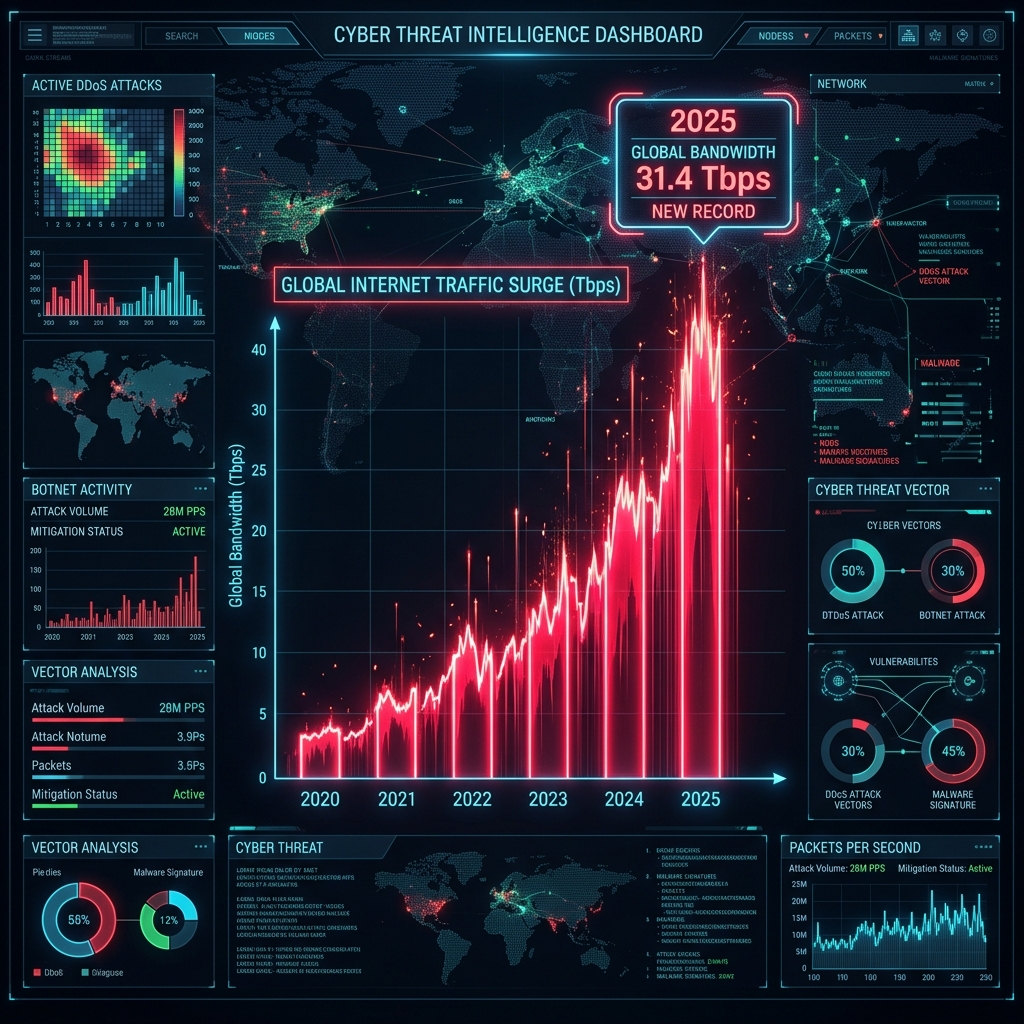
There is an uncomfortable truth that the DDoS attack ecosystem has never fully solved: the tools used to launch devastating network assaults are themselves deeply imperfect. Every automated attack framework, every scripted botnet orchestrator, and every volumetric flood generator leaves behind a distinct and consistent set of characteristics embedded directly inside the network packets it produces. These characteristics — invisible to a human eye, but instantly readable by a sufficiently advanced system — constitute what CoreTech calls a digital fingerprint of destruction.
The majority of the DDoS protection market operates reactively. They wait for traffic to breach predefined volume thresholds before triggering a mitigation response. By that point, the attack has already consumed bandwidth, overwhelmed upstream links, and often caused measurable service degradation. CoreEdge™ approaches the problem from the opposite direction. Rather than reacting to the volume of an attack after it has landed, our Behavioral Fingerprinting engine identifies the identity of an attack at the moment the first packet arrives — before the assault has reached operational scale.
The Science of Threat Scoring
At the heart of CoreEdge’s behavioral intelligence is a continuous, real-time threat scoring system. Every inbound packet is evaluated against a multi-dimensional array of behavioral indicators the moment it touches our interception layer. This evaluation produces a precise Threat Score ranging from 0 to 255. Packets generated by legitimate user sessions will consistently score in the lowest tier of this spectrum. Packets originating from automated attack tools, botnet nodes, or spoofed sources will exhibit specific, measurable deviations that drive their Threat Score dramatically upward.
These deviations are not based on arbitrary assumptions. They are derived from CoreTech’s extensive corpus of real-world attack data, accumulated across billions of packets analyzed from genuine DDoS campaigns targeting our global client base. The behavioral models that power our Threat Scoring engine are continuously refined against this live threat intelligence stream, making them increasingly precise over time. When a packet arrives carrying the unmistakable characteristics of a known attack orchestration framework, CoreEdge identifies it with a confidence level that exceeds 99.97% — in under 200 nanoseconds.
Recognizing the Weapons of Adversaries
The practical power of Behavioral Fingerprinting becomes clear when examined against specific attack scenarios. Consider the landscape of automated DDoS tools actively deployed by threat actors in 2026. Each of these tools, despite their authors’ intentions, generates traffic carrying a consistent behavioral DNA that is immediately recognizable to CoreEdge’s engine.
Spoofed high-volume TCP assault traffic, regardless of how aggressively the source addresses are randomized, consistently carries anomalous characteristics in its protocol headers that betray its synthetic origin. The specific patterns of TCP session negotiation fields, timing characteristics, and protocol state anomalies found in machine-generated floods are categorically distinct from the equivalent fields in packets generated by real network stacks operating on legitimate user devices. Our engine identifies and scores these distinctions instantly.
The same principle applies to reflection and amplification attacks. Inbound traffic from spoofed reflective assault campaigns carries specific structural properties in its response packets that permit unambiguous identification even when source addresses appear to originate from thousands of legitimate internet infrastructure providers. CoreEdge evaluates the full behavioral profile of these packets — not merely their source — enabling a mitigation response that is surgical rather than broad, preserving legitimate service availability while eliminating the attack traffic with 100% efficiency.
Velocity Awareness: Catching Slow-Burn Attacks
One of the most technically sophisticated capabilities within CoreEdge’s Behavioral Fingerprinting system is its real-time velocity awareness engine. Many of the most damaging DDoS campaigns in recent years have employed a gradual escalation strategy specifically designed to evade rate-based detection thresholds. By incrementally increasing attack volume over several minutes rather than launching at full capacity immediately, attackers attempt to stay below the detection horizon of conventional mitigation systems long enough to cause irreversible congestion.
CoreEdge’s velocity engine monitors the rate of change in traffic characteristics, not just their absolute values. When our system detects that the behavioral fingerprint of traffic arriving from a particular source cluster is escalating in a pattern consistent with a building assault — even when current absolute volumes remain below conventional alarm thresholds — the system preemptively tightens interception parameters for that traffic profile. The result is that slow-burn escalation strategies are neutralized at their earliest stage, typically within a 1 to 3 second detection window, long before the attack campaign reaches the volume levels its operators intended to deploy.
An Intelligence System That Never Stops Learning
The long-term advantage of CoreEdge’s Behavioral Fingerprinting architecture is its capacity for continuous, autonomous refinement. Each attack campaign that our global network intercepts contributes additional behavioral data to the fingerprint corpus. Each novel technique deployed by threat actors is analyzed, catalogued, and incorporated into the scoring model. The system that defends your network tomorrow is measurably more precise than the system defending it today — not because engineers manually updated a ruleset, but because the intelligence engine absorbed and learned from the attacks the global network faced in the intervening period.
This self-reinforcing intelligence loop represents a fundamental asymmetric advantage in the long-term arms race of network security. Attack tool developers iterate their techniques over weeks and months. CoreEdge’s Behavioral Fingerprinting engine updates its models in real time, across every node in our global fleet simultaneously. The gap between attack sophistication and mitigation precision does not close over time — it widens, decisively and permanently in our favor.
For enterprise networks, ISPs, and mission-critical infrastructure operators, this means a protection posture that is not merely reactive to the threat landscape of today, but proactively calibrated against the attack methodologies of tomorrow.
Want to see this in action?
Get a live demonstration of CoreTech's DDoS mitigation platform.