As we reflect on the state of global network security, 2025 will be remembered as a watershed moment in the evolution of Distributed Denial of Service (DDoS) attacks. The threat landscape underwent a dramatic and dangerous shift. Attackers abandoned long, drawn-out attrition campaigns in favor of devastating, short-burst hyper-volumetric strikes.
Fueled by the proliferation of sophisticated IoT botnets, unpatched cloud infrastructure, and the massive bandwidth capabilities of 5G networks, threat actors launched the most complex campaigns the internet has ever seen.
This report synthesizes global telemetry data, providing a definitive look at the numbers, trends, and tactical shifts that defined 2025.
1. The 2024 vs. 2025 Threat Matrix
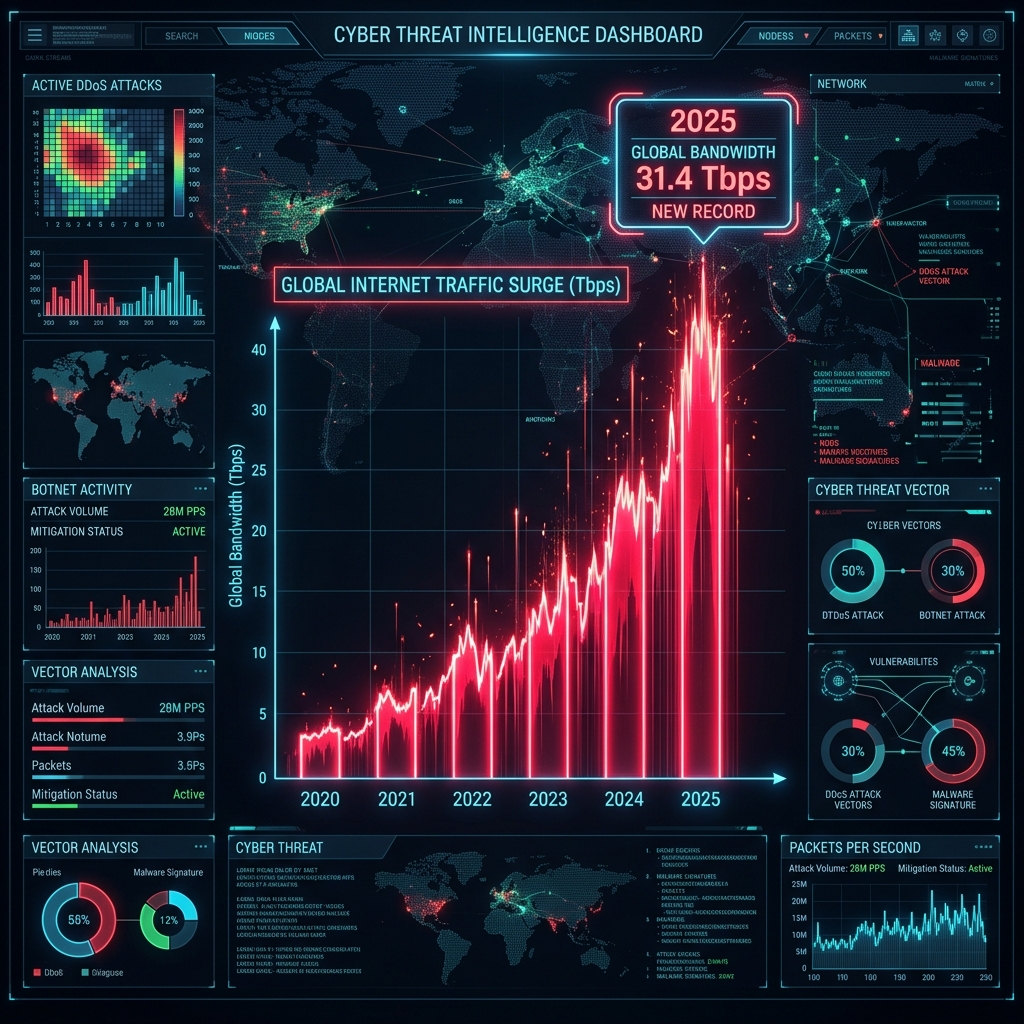
The year-over-year growth in attack metrics demonstrates an exponential increase in both scale and frequency. Below is a comparative snapshot of the global DDoS landscape:
| Key Metric | 2024 Benchmark | 2025 Record | Year-over-Year Growth |
|---|---|---|---|
| Total Global Attacks | ~21.3 Million | 47.1 Million | +121% |
| Peak Attack Bandwidth | 3.98 Tbps | 31.4 Tbps | +688% |
| Peak Request Rate (RPS) | 71 Million RPS | ~201 Million RPS | +183% |
| Average Attack Duration | 45 Minutes | < 10 Minutes | Shift to Short-Burst |
| Hourly Attack Average | ~2,430 | 5,376 | +121% |
2. The Volume Explosion: 47.1 Million Attacks
The barrier to entry for launching DDoS attacks has never been lower. The democratization of DDoS-for-hire platforms (booters) and the availability of sophisticated exploit kits have made launching high-volume attacks incredibly cheap.
According to global telemetry data from leading cybersecurity networks, including Cloudflare and Netscout, the total number of mitigated DDoS attacks in 2025 more than doubled to an astonishing 47.1 million.
Global Attack Volume Growth (Millions)
3. The 31.4 Tbps Barrier is Shattered
For years, the cybersecurity industry monitored the slow, linear upward creep of peak attack bandwidth. In late 2025, that linear growth curve was completely shattered.
The global bandwidth record was broken multiple times throughout the year, culminating in a historic 31.4 Tbps (Terabits per second) attack in the fourth quarter. This hyper-volumetric strike was fueled by an advanced variant of the Mirai botnet, composed of millions of compromised home routers, IP cameras, and smart TVs.
At its peak, this botnet bypassed traditional hardware firewalls by exhausting their state tables within milliseconds, proving that legacy connection tracking is no longer viable against modern botnets.
4. The Era of the “Short Burst”
Perhaps the most tactically significant shift in 2025 was the duration of attacks.
Attackers know that traditional, reactive mitigation services (which rely on human intervention or BGP ‘swinging’) take anywhere from 5 to 15 minutes to fully activate. By the time a legacy shield is deployed, a massive 5-minute attack has already caused severe downtime, and the attackers have moved on.
2025 Attack Duration Breakdown:
- 🔴 Less than 10 minutes:
89.3%(Highly tactical, designed to bypass reactive defenses) - 🟡 10 to 60 minutes:
8.1%(Standard attrition floods) - 🟢 Over 1 hour:
2.6%(Extortion and targeted political campaigns)
This data proves that manual mitigation is dead. If your defense system takes 5 minutes to scrub traffic, you are vulnerable directly in the window where 89% of attacks occur.
5. Prime Targets by Industry
While no sector is immune, 2025 saw a distinct shift in targeting behavior. Attackers followed the money and global infrastructure trends.
| Rank | Industry Sector | Traffic Share | Primary Motivation |
|---|---|---|---|
| 1 | Telecommunications & ISPs | 28% | Disrupting upstream infrastructure via Carpet Bombing. |
| 2 | AI Computing & Cloud Ops | 22% | Extortion against high-value, high-compute AI startups. |
| 3 | Financial Services | 18% | Ransom DDoS (RDDoS) and smokescreening for data breaches. |
| 4 | Gaming Server Hosting | 15% | Competitive disruption and UDP amplification floods. |
| 5 | Government & Public Sector | 10% | Hacktivism and geopolitical disruption. |
| 6 | Other Sectors | 7% | Collateral damage or isolated grievances. |
Notably, DDoS traffic directed at AI computing companies and their API endpoints saw massive spikes—increasing by as much as 347% month-over-month in late 2025.
Preparing for the Future with CoreEdge
The statistics from 2025 prove one thing definitively: reactive, fixed-capacity mitigation is obsolete.
When a volumetric attack can peak at 31.4 Tbps and conclude entirely within 5 minutes, organizations cannot survive relying on manual routing algorithms or hardware firewalls that exhaust their memory tracking 32-byte connections.
CoreTech’s global CoreEdge architecture is built precisely for this new reality:
- Zero-Second Mitigation: We do not rely on 5-minute BGP reroutes. Traffic is scrubbed inline instantly.
- eBPF/XDP Integration: Drop rules are applied at the kernel level, enabling terabit-scale blocking with absolutely zero CPU overhead.
- Microsecond Behavioral Fingerprinting: Instead of matching static signatures, our AI engine identifies malicious connection patterns and neutralizes them in a millisecond, completely preventing state-exhaustion.
The threats of 2025 set a new, terrifying benchmark. To ensure your business integrity, internet operations must be protected by technology built for the scale of 2026 and beyond.
Want to see this in action?
Get a live demonstration of CoreTech's DDoS mitigation platform.