DDoS attacks aren’t slowing down. In fact, they’re growing larger, smarter, and more frequent than ever. If your protection strategy hasn’t evolved since last year, you’re already behind.
Here are the most significant DDoS attack trends we’re tracking in 2026 — and what they mean for your business.
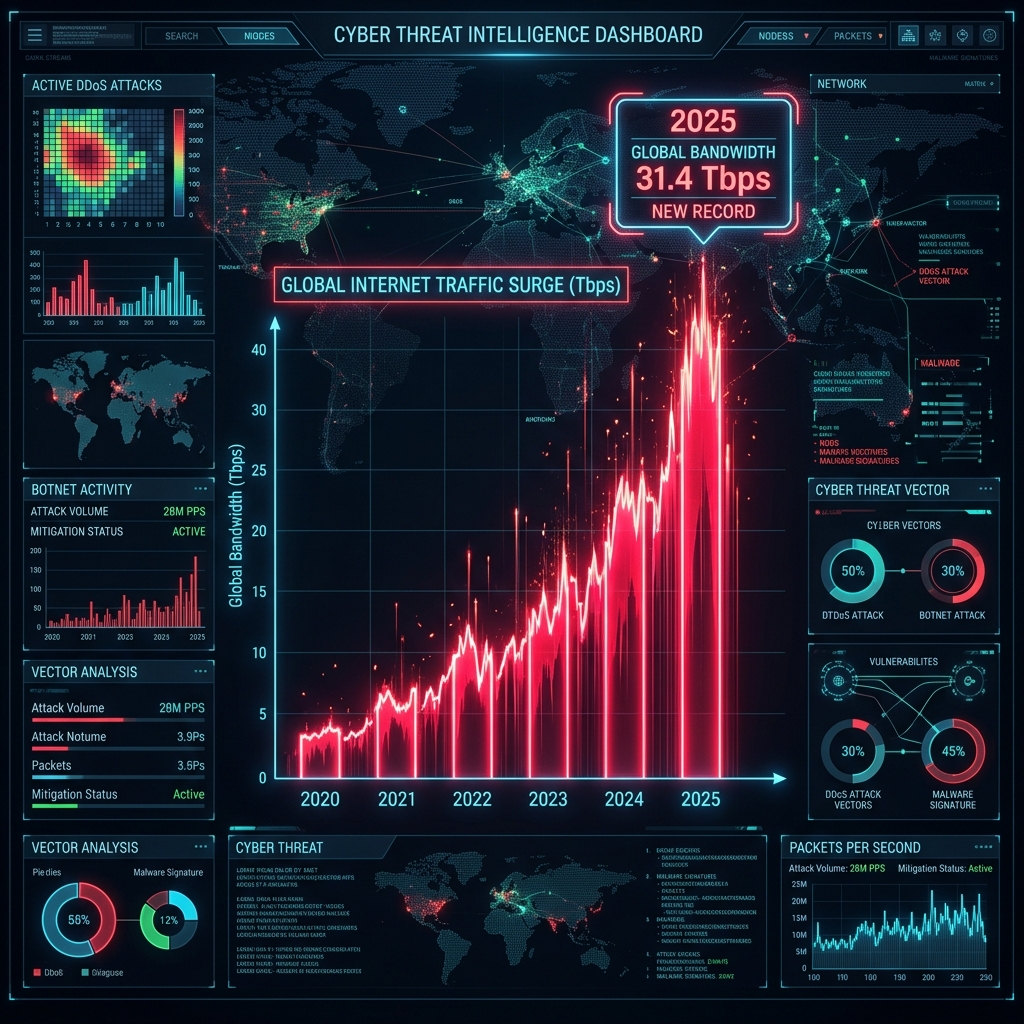
1. Attack Sizes Have Crossed the Terabit Barrier
What used to be headline news is now routine. Multi-terabit attacks are no longer rare events — they’re happening weekly across the internet.
What’s driving this:
- Millions of poorly secured IoT devices (cameras, routers, smart home systems) being weaponized into massive botnets
- DNS and NTP amplification techniques that multiply a small request into hundreds of gigabits of traffic
- “DDoS-for-hire” services making terabit-scale attacks accessible to anyone for under $50
What this means for you: If your DDoS mitigation provider can’t absorb multi-terabit attacks without performance degradation, you’re at risk. Ask your provider for their real-world filtering capacity — not their marketing number.
At CoreTech, our CoreEdge™ platform processes packets at wire speed on hardware-accelerated SmartNICs, handling terabit-scale attacks without any added latency to your legitimate traffic.
2. Layer 7 (Application) Attacks Are Surpassing Volumetric Floods
The biggest shift in 2026 is the move from brute-force bandwidth attacks to intelligent application-layer attacks. These are harder to detect and harder to stop.
What’s changing:
- HTTP/HTTPS floods that mimic real user behavior — correct headers, valid cookies, realistic browsing patterns
- API abuse attacks targeting login endpoints, checkout pages, and search functions
- Slow-and-low attacks (like Slowloris) that consume server resources without generating enough bandwidth to trigger traditional detectors
- Credential stuffing at scale — automated login attempts using leaked password databases
Why traditional defenses fail: Volumetric detection systems only look at bandwidth and packets per second. A sophisticated L7 attack can overwhelm your application with just 5,000 requests per second — well below any bandwidth threshold.
CoreDetection™ analyzes traffic behavior, not just volume. It identifies L7 attacks by recognizing bot-like patterns, suspicious request timing, and protocol anomalies — blocking bots while allowing real users through.
3. Multi-Vector Attacks Are Now the Standard
Attackers in 2026 don’t rely on a single method. Modern DDoS campaigns combine multiple attack vectors simultaneously:
- L3/L4 volumetric flood to overwhelm your network bandwidth
- L7 HTTP flood to exhaust your web servers
- DNS attack to take down your domain resolution
- Targeted API abuse to overload specific application functions
The goal is to overwhelm security teams with multiple simultaneous threats, making it harder to respond to any single one.
What this means for you: You need protection that covers every layer — not just bandwidth filtering. If your DDoS mitigation only handles L3/L4, your applications are exposed.
CoreTech’s dual-engine architecture — CoreDetection™ for intelligent analysis and CoreEdge™ for wire-speed filtering — protects at every layer from L3 through L7, identifying and mitigating each vector independently.
4. AI-Powered Botnets Are Getting Smarter
The most alarming trend of 2026: attackers are using AI to make their botnets harder to detect.
What we’re seeing:
- Bots that adapt their behavior in real-time to evade detection
- Traffic patterns that closely mimic legitimate human browsing
- Automated attack tools that test a target’s defenses and adjust their approach
- Geographic distribution that matches a target’s real user base, making source-based filtering ineffective
Why this matters: Static detection rules can’t keep up with adaptive attacks. If your protection relies on fixed signatures or simple rate limits, AI-powered botnets will evade it.
CoreDetection™ uses behavioral analysis that looks at how traffic moves, not just what it looks like. Even AI-generated bot traffic exhibits patterns that differ from real users — and CoreDetection™ catches them.
5. The Gaming and Esports Industry Remains a Top Target
Online gaming continues to be one of the most attacked sectors in 2026. The reasons are simple: games are latency-sensitive, always online, and the community has a culture of competitive disruption.
The gaming threat landscape:
- Game server targeting — taking competitors offline during tournaments
- Player IP exposure — voice chat and P2P connections leaking player addresses
- Ransom DDoS — “pay us or we take your servers down during your biggest event”
- UDP protocol abuse — most game traffic is UDP, making it easy to flood
What gaming companies need: Sub-millisecond mitigation latency. If your DDoS protection adds 20ms of latency, players will leave. You need filtering that happens at the network interface level — invisible to players.
CoreEdge™ processes packets at the NIC hardware level, adding zero latency to clean traffic. Gaming companies using CoreTech experience no difference between protected and unprotected gameplay.
6. Ransom DDoS Is a Growing Business Model
“Pay us $10,000 in Bitcoin or we’ll take your business offline for 24 hours.”
Ransom DDoS (RDDoS) has become a structured criminal business in 2026. Attackers send demand letters, demonstrate their capability with a brief attack, and then threaten sustained disruption.
The trend:
- Ransom demands are getting smaller (to increase the likelihood of payment)
- Attackers are targeting smaller businesses that are less likely to have protection
- Some groups are now offering “protection rackets” — monthly payments to not be attacked
- Payment doesn’t guarantee safety — many victims are attacked again after paying
The only defense: Having mitigation in place before the threat arrives. Once you’re under ransom DDoS, scrambling to find protection is already too late.
CoreTech offers same-day emergency onboarding via GRE tunnel. If you’re under active attack, we can have you protected in under 30 minutes.
7. Cloud Infrastructure Is Increasingly Targeted
As more businesses move to the cloud, attackers follow. Cloud-hosted services, SaaS platforms, and cloud-native applications are prime DDoS targets in 2026.
Why cloud is vulnerable:
- Shared infrastructure means an attack on one tenant can affect others
- Cloud providers offer basic DDoS protection, but it’s often insufficient for sophisticated attacks
- Auto-scaling during an attack can generate massive unexpected bills (“economic DDoS”)
- Many cloud deployments lack the network-level protection that on-premises infrastructure has
What cloud-native businesses need: BGP-level protection that sits in front of your cloud infrastructure. Not a reverse proxy. Not a WAF. Real network-layer mitigation that filters traffic before it reaches your cloud provider.
CoreTech protects cloud infrastructure via BGP over GRE tunnel — no hardware required, deployed in minutes, and fully compatible with AWS, GCP, Azure, OVH, and Hetzner.
8. Regulatory Pressure Is Increasing
Governments are taking DDoS more seriously in 2026. Financial institutions, healthcare providers, and critical infrastructure operators face increasing regulatory requirements around DDoS resilience.
Emerging requirements:
- Mandatory DDoS mitigation plans for critical infrastructure sectors
- Incident reporting obligations — many jurisdictions now require DDoS attacks to be reported within 24-72 hours
- Business continuity audits that include DDoS attack scenarios
- Third-party risk assessments that evaluate your hosting and protection providers
What this means for you: DDoS mitigation is no longer optional — it’s becoming a compliance requirement. And regulators are looking for documented mitigation plans, SLA guarantees, and forensic reporting capabilities.
Every CoreTech customer gets full forensic data through the Client Portal: attack timelines, source analysis, mitigation metrics, and exportable reports — everything you need for compliance documentation.
How to Protect Your Business in 2026
The DDoS landscape is more dangerous than ever. Here’s what actually works:
✅ Multi-Layer Protection
Don’t just filter bandwidth. You need L3/L4 mitigation and L7 application protection working together.
✅ Behavioral Detection
Static thresholds won’t catch modern attacks. Choose a provider that uses behavioral analysis to distinguish real users from bots.
✅ Zero-Latency Mitigation
Your protection shouldn’t slow down your business. Hardware-accelerated filtering ensures legitimate traffic is unaffected.
✅ Full Visibility
If you can’t see what’s happening during an attack, you can’t make informed decisions. Real-time dashboards and forensic data are essential.
✅ SLA Guarantees
If your provider won’t put their mitigation commitments in writing, find one who will.
✅ Always-On Readiness
Don’t wait for an attack to scramble for protection. Have mitigation in place before you need it.
Stay Ahead of the Threat
CoreTech’s CoreDetection™ and CoreEdge™ are built for the 2026 threat landscape — behavioral AI detection, hardware-accelerated filtering, full L3-L7 coverage, and sub-minute mitigation.
Start your free 10-day trial and see why leading ISPs, gaming companies, and enterprises trust CoreTech to keep them online.
Want to see this in action?
Get a live demonstration of CoreTech's DDoS mitigation platform.